Setting up SAML with Okta
The following example may be useful if you are using Okta as a SAML identity provider. Note that Okta does not support service provider-signed requests even if they are enabled on the SonarQube side.
To integrate Okta (identity provider) with SonarQube (service provider), both sides need to be configured.
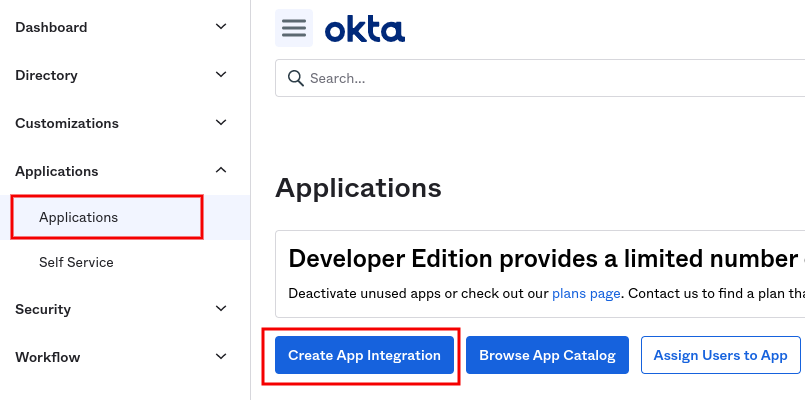
Create a new application in the Okta admin dashboard
Step 1: Under Applications, select Create App Integration.
Step 2: Choose SAML 2.0 in the Sign-in Method dialog.
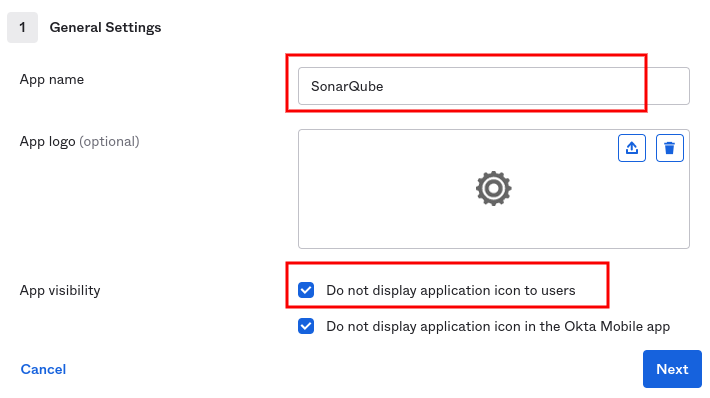
Step 3: Under General Settings, fill in the App name with SonarQube (or another name that you prefer), and select Do not display application icon to users.
Configure SAML settings
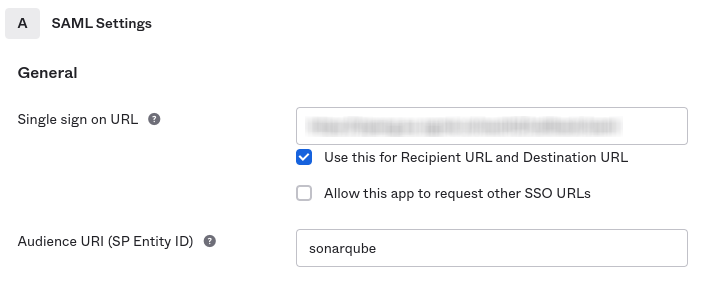
Step 1: Under General Settings, configure the following fields:
- Single sign on URL:
<Your SonarQube URL>/oauth2/callback/saml(e.g.,https://sonarqube.mycompany.com/oauth2/callback/saml). - Audience URI (SP Entity ID): Something like
sonarqube(SonarQube default value). It must not contain whitespace.
Step 2: An assertion signature is mandatory. You must keep the following default settings in Show Advanced Settings:
- Response: Choose Signed.
- Assertion Signature: Choose Signed.
- Signature Algorithm: Choose RSA-SHA256.
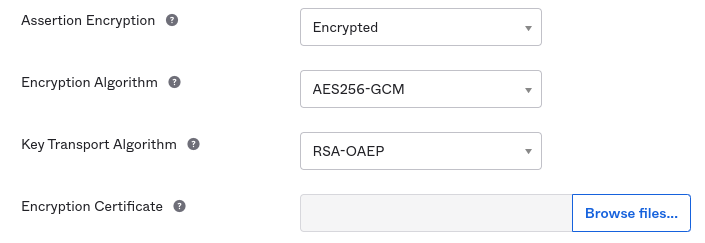
Step 3: (Optional) If you want to enable assertion encryption, expand Show Advanced Settings and configure the following fields:
- Assertion Encryption: Choose Encrypted.
- Encryption Algorithm: Choose AES256-GCM for high security.
- Key Transport Algorithm: Choose RSA-OAEP.
- Encryption Certificate: Add the service provider certificate. It should be the same certificate as the one found in the SonarQube SAML settings under Service provider certificate.
Step 4: Under Attribute Statements, add the following attribute mappings:
- Create a mapping for the name:
- Name:
name. - Name format: Unspecified.
- Value: Choose
user.firstName.
- Name:
- Create a mapping for the login:
- Name:
login. - Name format: Unspecified.
- Value: Choose
user.login.
- Name:
- (Optional) Create a mapping for the email:
- Name:
email. - Name format: Unspecified.
- Value: Choose
user.email.
- Name:
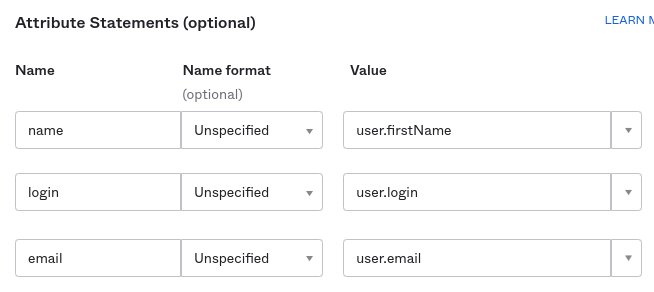
- (Optional) Under Group Attribute Statements (See details in Group synchronization):
- Name:
groups. - Name format: Unspecified.
- Filter: Choose Matches regex and set the value to
.*.
- Name:
Step 5: Select Finish in the Feedback dialog to confirm the creation of the application.
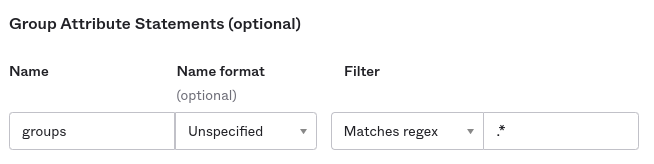
Step 6: You can now add users and groups in the Assignments tab of the application.
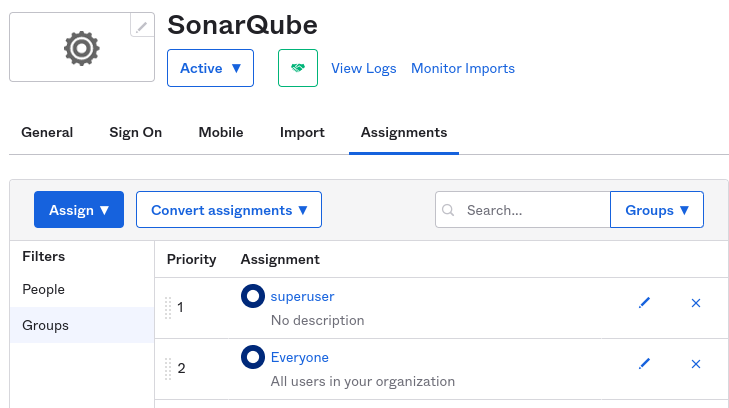
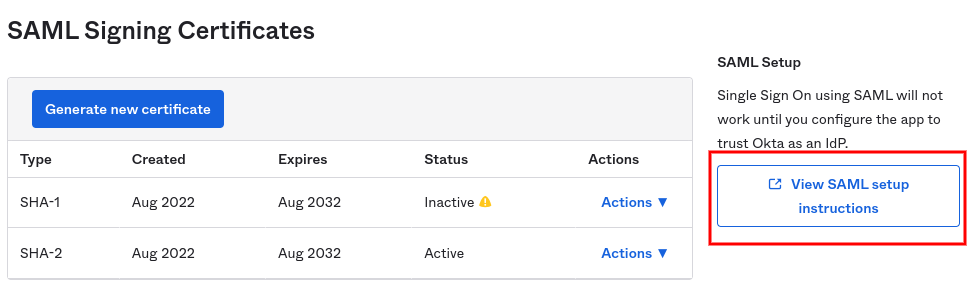
Step 7: Navigate to the Sign On tab of the SonarQube application in Okta.
Step 8: Next to the SAML Signing Certificates subsection, you will find the configurations needed for setting up SonarQube, under View SAML setup instructions.
In SonarQube, Configure SAML authentication
- Go to Administration > Configuration > General Settings > Authentication > SAML.
- Select Create configuration. A dialog opens.
- Provide the fields below:
- Application ID: The value of the Audience URI (SP Entity ID) you set in Okta (for example,
sonarqube). - Provider ID: The value of Identity Provider Issuer provided in View SAML setup instructions from Okta.
- SAML login URL: The value of Identity Provider Single Sign-On URL provided in View SAML setup instructions from Okta.
- Identity provider certificate: The value of X.509 Certificate provided in View SAML setup instructions from Okta.
- SAML user login attribute:
login(or whatever you configured above when doing the mapping). - SAML user name attribute:
name(or whatever you configured above when doing the mapping). - (Optional) SAML user email attribute:�
email(or whatever you configured above when doing the mapping). - Sign requests: Not supported for Okta.
- (Optional) Service provider private key: The private key is required for assertion encryption support. It must be provided for SonarQube in
PKCS8format without encryption. You can find instructions for converting to different key formats here. - (Optional) Service provider certificate: The certificate is required for assertion encryption support. It must be shared with Okta in order to activate the assertion encryption.
- Application ID: The value of the Audience URI (SP Entity ID) you set in Okta (for example,
The service provider private key and certificate can be either a new self-signed pair or any existing pair available in your infrastructure.
Enabling and testing SAML authentication
Step 1: Save the SAML configuration by clicking Save configuration
Step 2: Before enabling the SAML authentication on SonarQube, you can verify that the configuration is correct by clicking on Test Configuration. A SAML login will be initiated and useful information about the SAML response obtained from the Identity provider will be returned.
Step 3: enable the configuration by clicking Enable configuration.
Step 4: In the login form, the new button Log in with Okta (or a custom name specified in the Provider Name field) allows users to connect with their SAML account.
Group synchronization
You can enable the group synchronization feature in SonarQube, provided you have configured a groups attribute in your Okta application (see above). For more information about this feature, see SAML group synchronization in SAML overview.
To enable the group synchronization in SonarQube:
- Go to Administration > Configuration > General Settings > Authentication > SAML.
- Select the Edit button to open your SAML Okta configuration.
- In SAML group attribute, enter
groups, or the name you gave to this attribute in your Okta Application. - Select Save configuration.
Enabling SCIM provisioning
Starting in Enterprise Edition, once you’ve set up Okta as your SAML Identity Provider, you can set up SCIM provisioning to automate user and group provisioning within Okta.
For more information, see SCIM provisioning in Okta.
Was this page helpful?