GitHub code scanning alerts for security vulnerabilities
This feature is only available in the Enterprise plan.
SonarQube Cloud automatically provides feedback about security vulnerabilities inside the GitHub interface itself. Security vulnerabilities found by SonarQube Cloud will appear both as part of the analysis results displayed in the SonarQube Cloud interface and as GitHub Scanning Alerts under the Security tab in the GitHub interface.
Security vulnerabilities surfaced as code scanning alerts
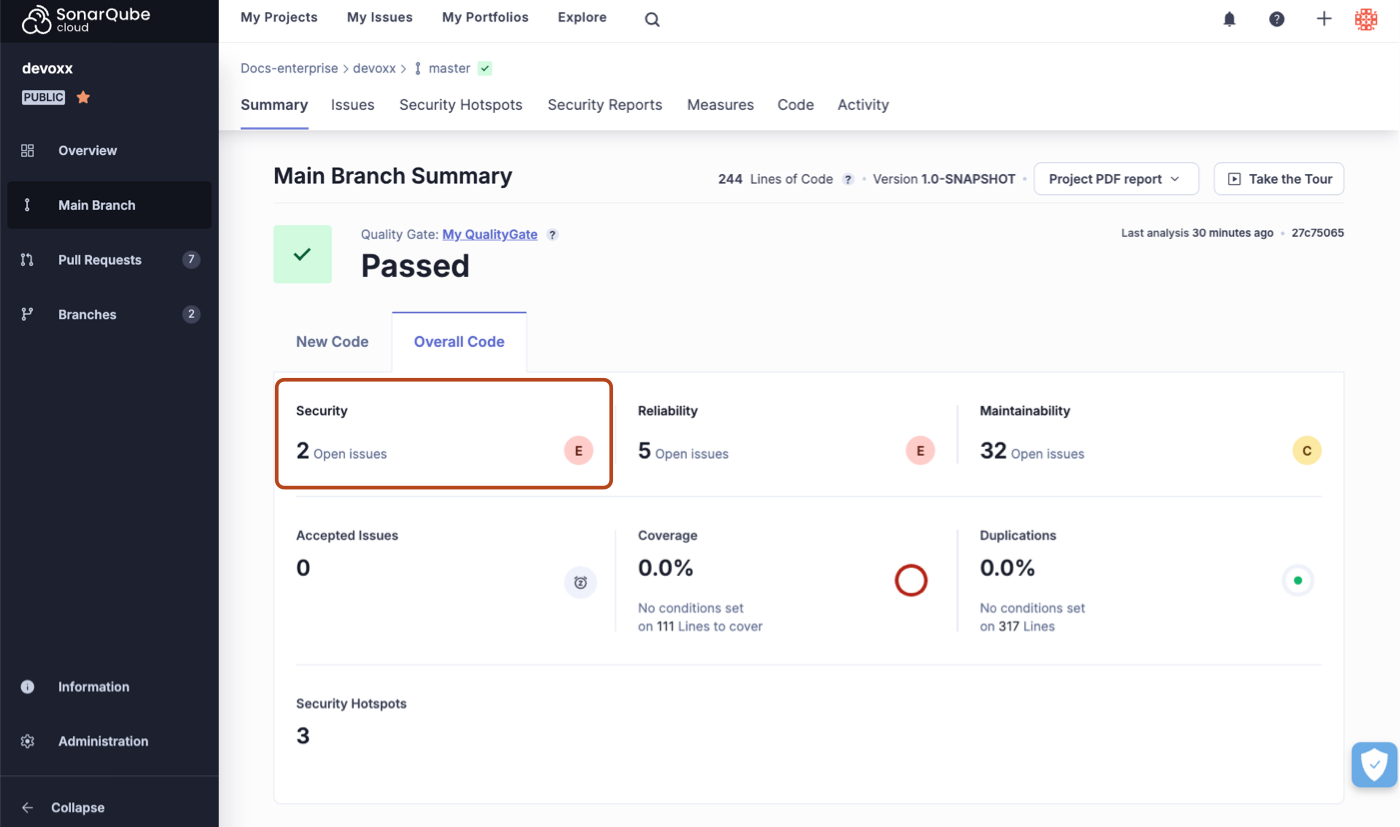
When you perform an analysis on a project, the security vulnerabilities found will be displayed in the SonarQube Cloud interface:
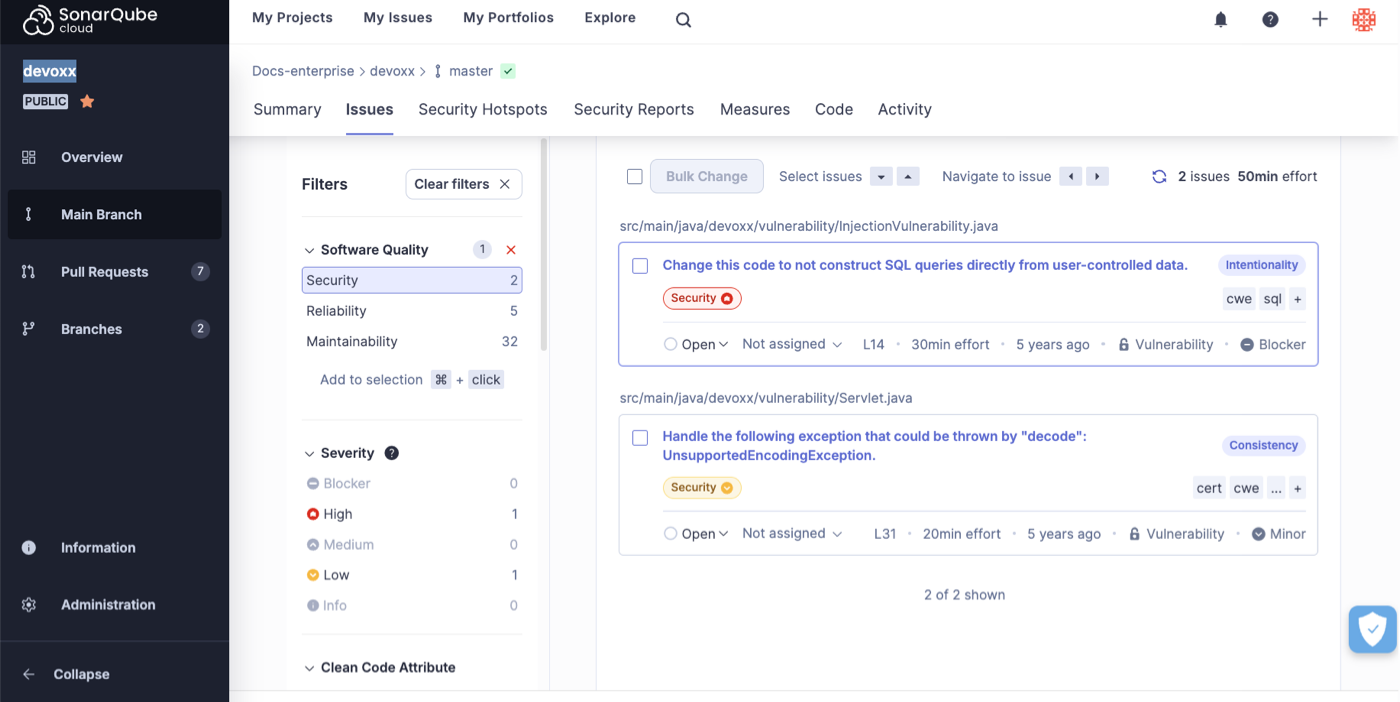
You can click on the counter to display a list of detected security vulnerabilities:
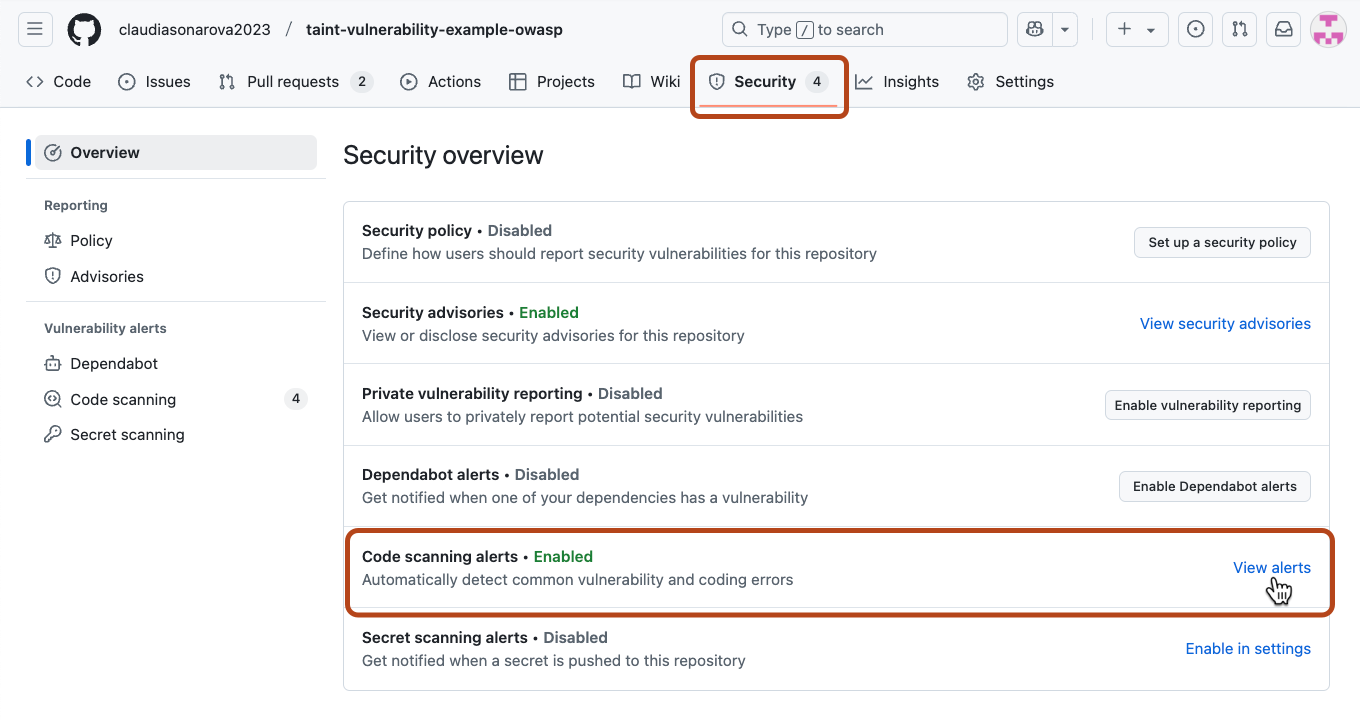
If your project is in GitHub you will also find the same security vulnerabilities displayed within the GitHub interface under the Security Tab. Select View alerts to see the full list.
Bi-directional synchronized status changes
When you change the status of a security vulnerability in the SonarQube Cloud interface that status change will be immediately reflected in the GitHub interface and vice versa.
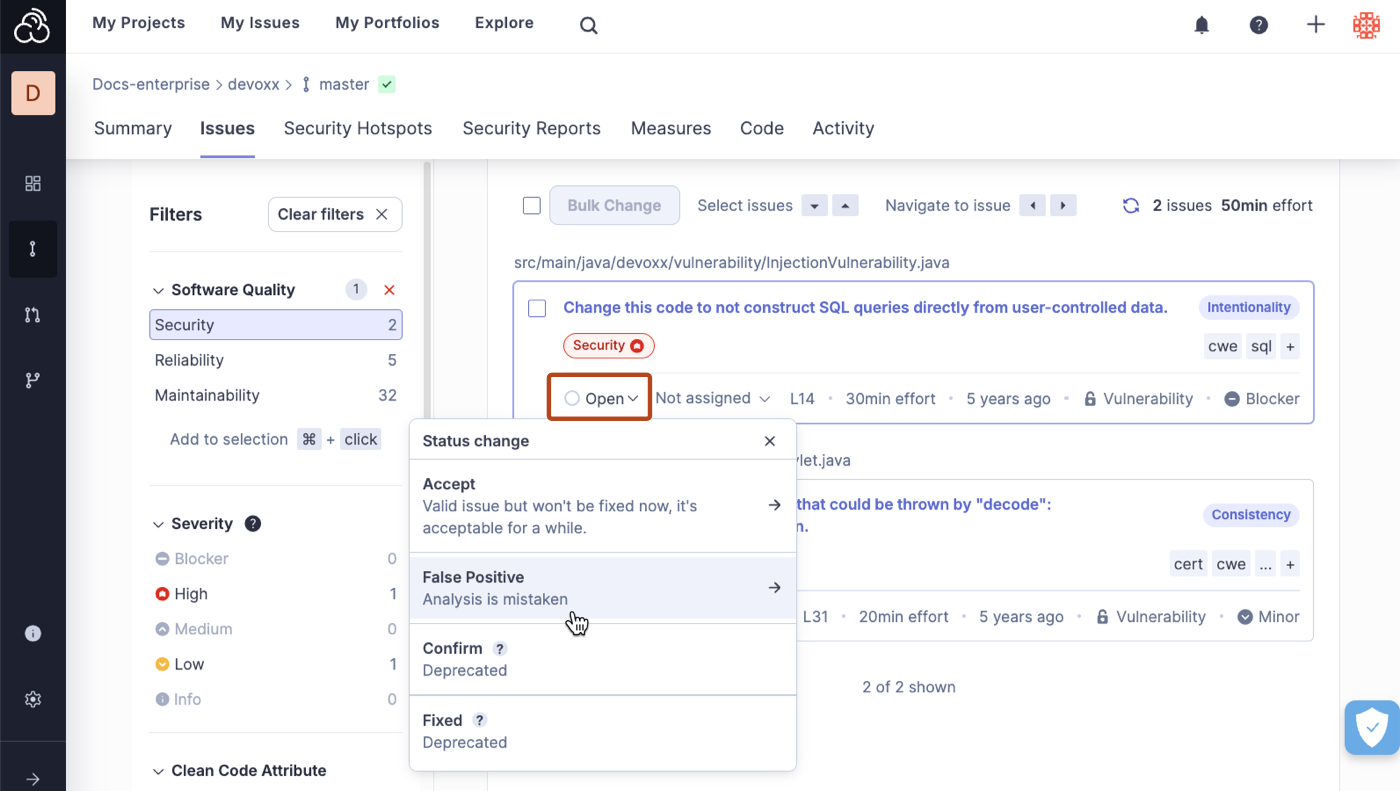
For example, if you change an issue from Open to False Positive here in SonarQube Cloud:
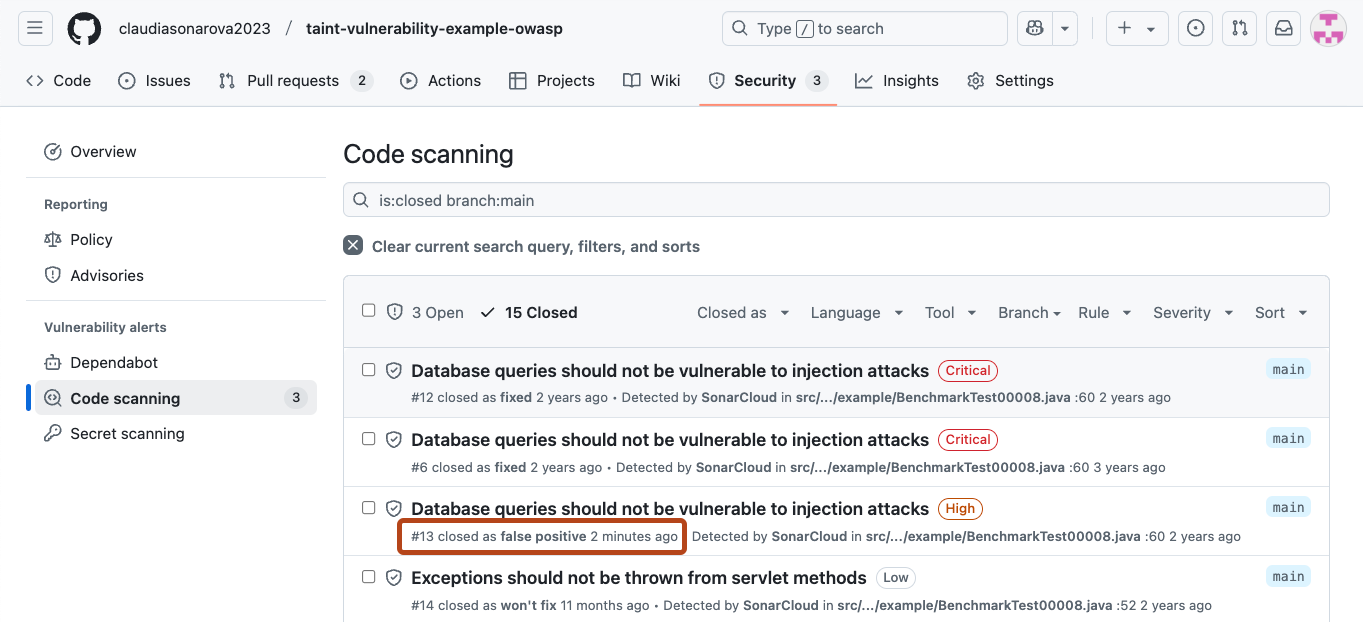
That change will be reflected in the code scanning alerts in GitHub:
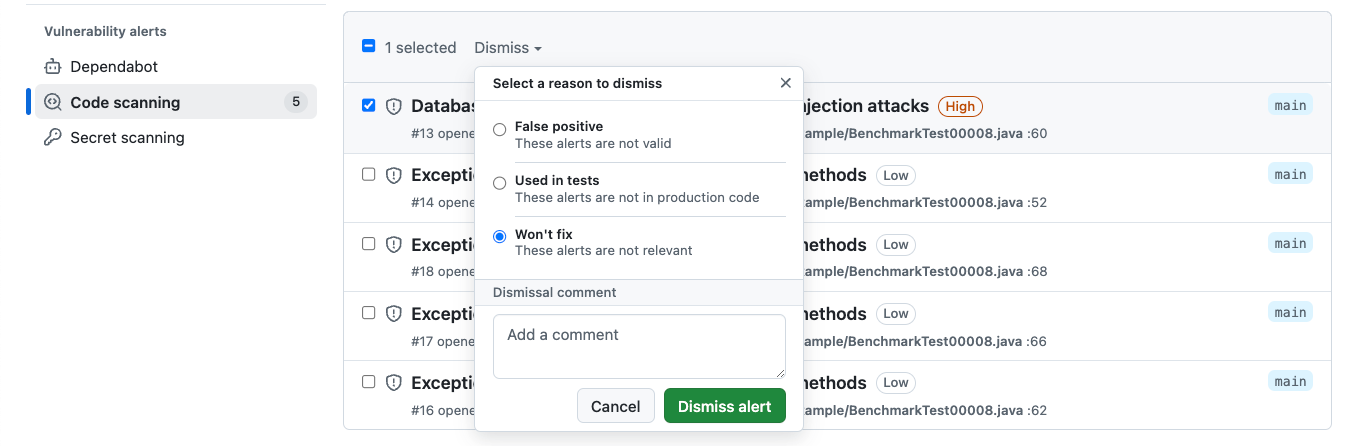
Similarly, if you change an issue from Open to Won't Fix in GitHub:
That change will be reflected in SonarQube Cloud.
Correspondence of statuses
Initially, all vulnerabilities marked Open on SonarQube Cloud are marked Open on GitHub. However, because the available statuses on the two systems are not exactly the same, the following logic is used to manage the transitions.
| On SonarQube Cloud, a transition to | results in this on GitHub |
|---|---|
| Accept | Won't fix |
| False Positive | False positive |
| Confirm (Deprecated) | Open |
| Fixed (Deprecated) | Open |
| Reopen | Open |
| On GitHub, a transition to | results in this on SonarQube Cloud |
|---|---|
| False positive | False Positive |
| Used in tests | Accept |
| Won't fix | Accept |
| Reopen | Open |
No configuration needed
You might notice a button in the GitHub Security tab labeled Add more scanning tools. This is used to configure third-party plugins. To use scanning alerts from SonarQube Cloud, however, you do not need to add any third-party plugins.
The GitHub Code Scanning Alerts for Security vulnerabilities feature is enabled automatically and for free on all public GitHub Repositories. You just have to make sure that your repository is bound to SonarQube Cloud (in other words you have to import it through the SonarQube Cloud interface).
To enable scanning alerts on a private GitHub repository you will need to pay for the GitHub Advanced Security feature. This is entirely on the GitHub side. SonarQube Cloud does not charge anything extra to enable the scanning alerts feature.
Managing access to security alerts
In GitHub, you can configure access to security alerts for your repository.
Was this page helpful?